Connection Modes
USP supports two connection modes that determine how inbound traffic from external clients is handled and forwarded to internal targets: Session Break Mode and Direct Mode.
These modes differ in how connections are terminated, authenticated, and relayed across the DMZ boundary. The selected mode determines the security boundary, configuration requirements, and operational characteristics of the deployment.
This page explains how each mode works, which configuration items are required, and how to determine which model best fits your security and operational requirements.
For available deployments that use Session Break Mode or Direct Mode, see Deployment Models.
Session Break Mode
Session Break Mode is a layered security model used in USP. In this mode:
- The USP Server terminates all inbound connections in the DMZ.
- The USP Server can optionally pre-authenticate the external session at the proxy.
- The USP Server establishes a separate outbound connection to the internal target initiated by the USP Client residing in the internal network.
Benefits include:
- Enforces authentication at the edge (DMZ boundary), stopping unauthorized clients before they ever reach the internal server.
- When configured to use ICAP, allows files to be inspected at the network perimeter before they enter the trusted network.
- Protocol visibility allows the proxy to detect and block malformed or anomalous commands before they reach internal systems.
- No partner or configuration data is ever stored in the DMZ, even temporarily.
- The internal target remains isolated behind a firewall without requiring inbound connections from the DMZ into the LAN.
- External clients do not connect directly to internal systems; the USP Server mediates access through distinct inbound and outbound sessions.
To use Session Break Mode, you must configure the following session-break Configuration Items:
- Route
- Inbound Node (with a mandatory IP Filter)
- Outbound Node
- Rule
- Listener
- Deployment
- Tunnel and Proxy Client
How It Works
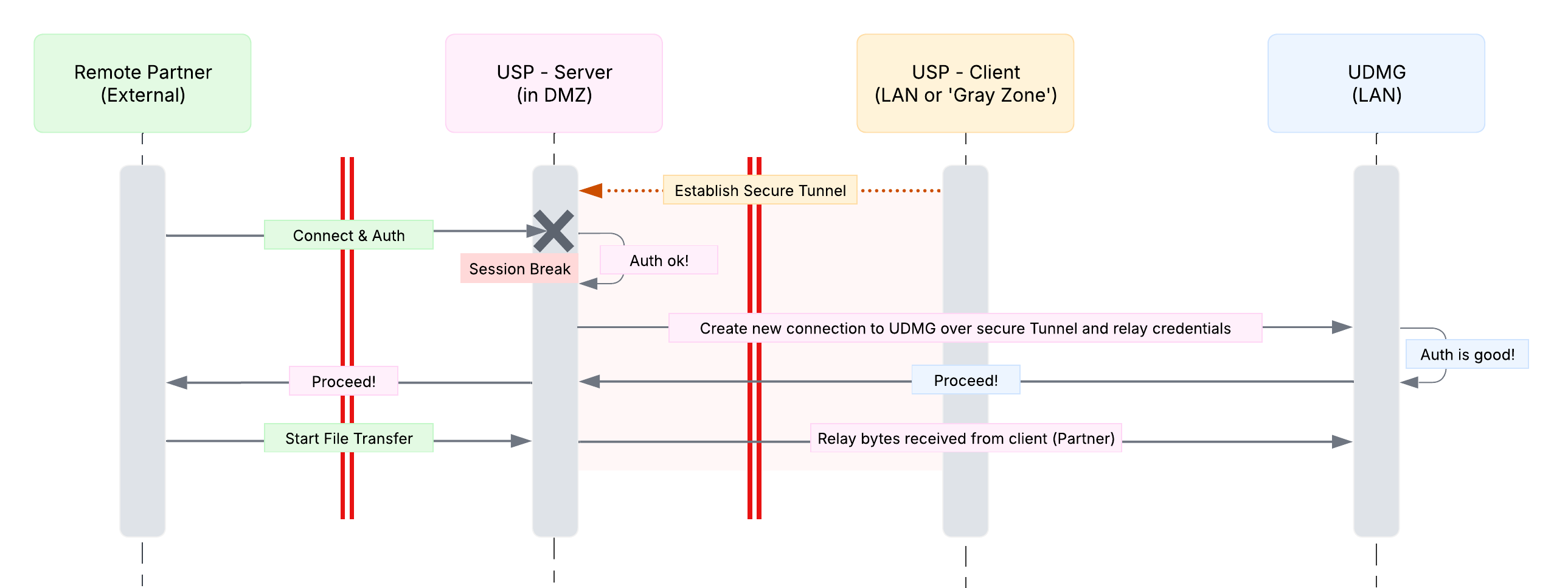
- An external client connects to the USP Server in the DMZ.
- The USP Server terminates the inbound connection at the DMZ boundary and can optionally authenticate the client at the proxy.
- The USP Server establishes a separate outbound connection to the internal target via a secure Tunnel initiated by the USP Client from the internal network.
- The internal target may perform its own authentication using either relayed credentials from the external client or credentials defined for the outbound connection.
- The inbound and outbound connections are linked, creating a session break between the external client and the internal target.
- Data is relayed between the external client and the internal target through the USP Server.
At no point does the external client connect directly to internal systems.
Direct Mode
Direct Mode enables USP to proxy TCP connections directly and securely to the target server. In this mode:
- USP accepts inbound TCP connections on a TCP Listener.
- USP establishes a TCP outbound connection and forwards packets received from the remote partner verbatim to the internal target through a secure Tunnel initiated by the USP Client residing in the internal network.
Benefits include:
- Maintains end-to-end cryptographic integrity (client keys, session keys, etc. stay exclusive with the client and internal server, allowing for public-key based authentication modes).
- Maintains full authentication fidelity, preserving all authentication methods supported by the internal target server.
- Is operationally simple to set up and maintain as there is no need to duplicate and maintain accounts, credentials, certificates, etc.
- The internal target remains isolated behind a firewall without requiring inbound connections from the DMZ into the LAN.
- No partner or configuration data is ever stored in the DMZ, even temporarily.
Unlike Session Break Mode, Direct Mode requires only the following Configuration Items:
- TCP Listener (with a mandatory IP Filter)
- TCP Deployment
- Tunnel and Proxy Client
How It Works
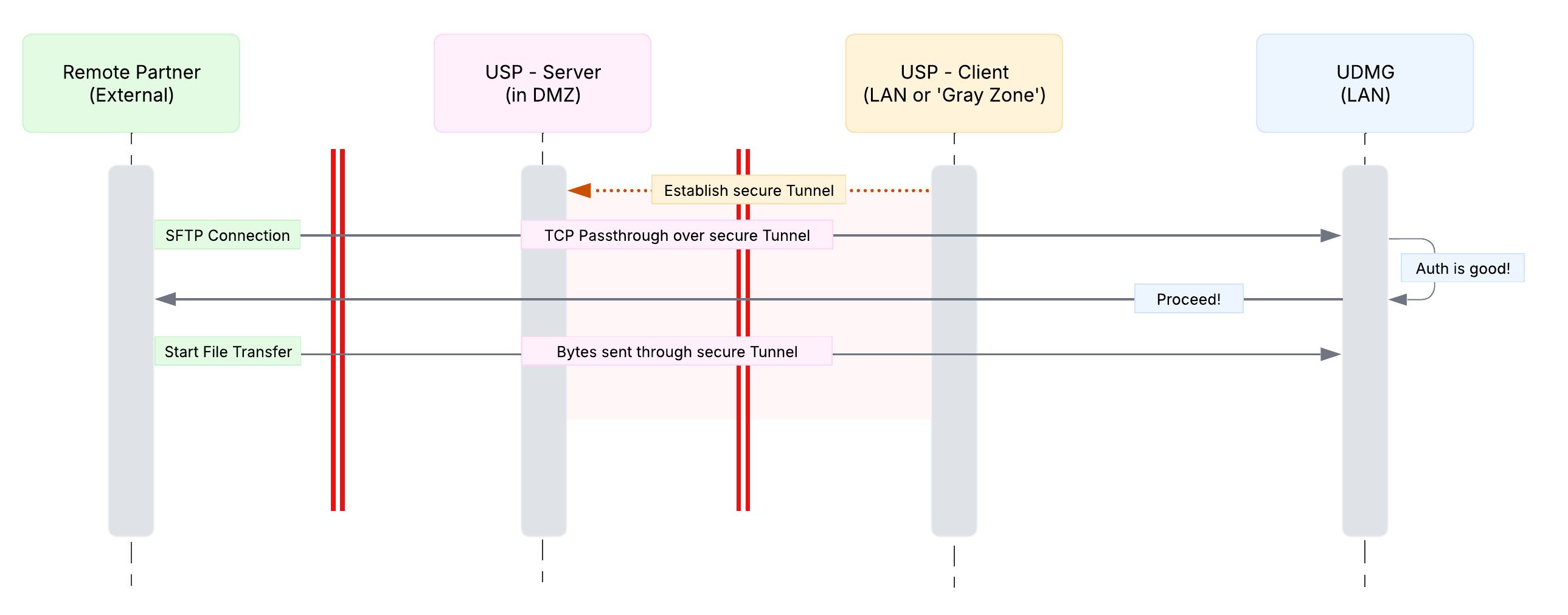
- An external client connects to the USP Server on the TCP Listener.
- The USP Server, hosted in the DMZ, accepts the inbound TCP connection and applies any configured IP filtering.
- The USP Server establishes a TCP connection to the configured outbound target via a secure Tunnel initiated by the USP Client from the internal network.
- The inbound and outbound TCP connections are "glued" together (no session break is performed).
- The external client never connects directly to internal systems.
At no point does the external client connect directly to internal systems.
Choosing the Right Mode
Session Break Mode and Direct Mode serve different security and operational goals.
Use the comparison below to evaluate the trade-offs between proxy-level enforcement (Session Break Mode) and end-to-end protocol passthrough (Direct Mode), and determine which model best fits your protocol requirements, security posture, and deployment constraints.
| Dimension | Session Break Mode | Direct Mode | Best Fit |
|---|---|---|---|
| Authentication Boundary | Authentication can be performed by USP and is typically also performed at the internal target. | Authentication is performed only by the internal target. | Session Break Mode |
| Authentication Method Fidelity | Limited to authentication methods that USP can terminate and replay. This excludes modes like Public Key only authentication, as that would require the client's private key. | Full fidelity: the internal target receives the original client authentication exchange and can use any authentication method it supports. | Direct Mode |
| Exposure of Backend | The internal target does not receive unauthenticated traffic. | The internal target receives the proxied client connection without proxy-level authentication. | Session Break Mode |
| Security Posture | Strong isolation; USP provides a clear security boundary at the edge of your network. | Reduced isolation; the security boundary shifts closer to the internal target. | Session Break Mode |
| Attack Surface | Smaller internal target attack surface; USP absorbs authentication abuse, scans, and connection floods; however, attack surface is now shifted to the DMZ. | Larger internal target attack surface; the internal target must handle malformed or abusive connections; however, this results in a reduced attack surface in the DMZ. | Session Break Mode |
| Operational Complexity | Higher: users, credentials, and policies must be managed in both USP and the internal target. | Lower: authentication and authorization are centralized in the internal target. | Direct Mode |
| Configuration Overhead | Higher onboarding and partner setup overhead. | No onboarding or partner setup overhead as those are managed at the internal target. | Direct Mode |
| Protocol Awareness at Proxy | USP must understand protocol semantics (for example, SFTP, FTPS, AS2). | USP is protocol-agnostic and forwards TCP connections only. | Direct Mode |
| Performance / Latency | Additional overhead due to session termination and re-establishment; however, in performance tests the additional overhead was negligible even over high volume transfers. | Lower overhead due to a single end-to-end session. | Direct Mode |
| Auditing and Visibility | Requires both proxy-level and internal target logging and monitoring. | Auditing is primarily handled at the internal target. | Direct Mode |
| Policy Enforcement Point | Policies can be enforced at USP and at the internal target. | Policies are enforced only at the internal target. | Tie |
| Failure Modes | More moving parts; configuration mismatches can result in authentication failures. | Fewer moving parts; failures are typically easier to diagnose. | Direct Mode |
| Compliance Narrative | Stronger alignment with DMZ isolation and proxy-level enforcement. Some organizations interpret certain PCI DSS requirements as requiring authentication at the DMZ. | May be acceptable depending on policy and compliance interpretation, but typically requires stronger hardening and monitoring at the internal target. | Session Break Mode |
| Use Case Fit | Extremely high-security environments with strict DMZ controls, layered defense, and regulated requirements. | Secure environments (for example, internal traffic flows or trusted partner networks) where reduced overhead is prioritized. | Session Break Mode |